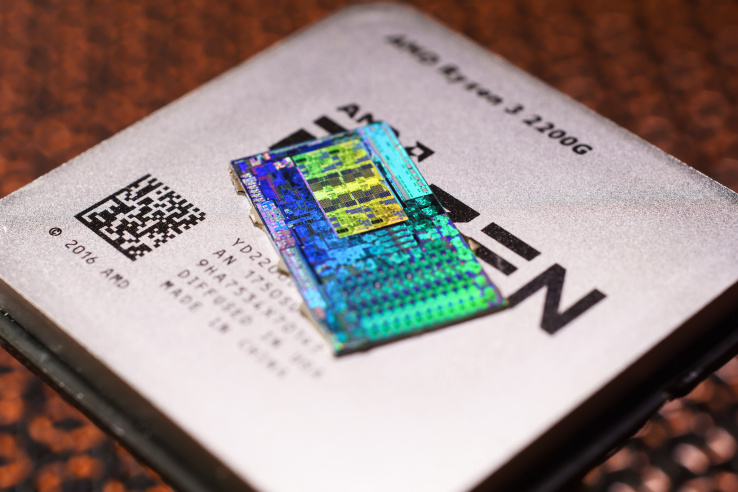
A newly discovered set of vulnerabilities in AMD chips is making waves not because of the scale of the flaws, but rather the rushed, market-ready way in which they were disclosed by the researchers. When was the last time a bug had its own professionally shot video and PR rep, yet the company affected was only alerted 24 hours ahead of time? The flaws may be real, but the precedent set here is an unsavory one.
The flaws in question were discovered by CTS Labs, a cybersecurity research outfit in Israel, and given a set of catchy names: Ryzenfall, Masterkey, Fallout, and Chimera, with associated logos, a dedicated website, and a whitepaper describing them.
So far, so normal: major bugs like Heartbleed and of course Meltdown and Spectre got names and logos too.
The difference is that in those cases the affected parties, such as Intel, the OpenSSL team, and AMD were quietly alerted well ahead of time. This is the concept of “responsible disclosure,” and gives developers first crack at fixing an issue before it becomes public.
There’s legitimate debate over just how much control big companies should exert over the publicity of their own shortcomings, but generally speaking in the interest of protecting users the convention tends to be adhered to. In this case, however, the CTS Labs team sprang their flaws on AMD fully formed and with little warning.
 The flaws discovered by the team are real, though they require administrative privileges to execute a cascade of actions, meaning taking advantage of them requires considerable access to the target system. The research describes some as backdoors deliberately included in the chips by Taiwanese company ASmedia, which partners with many manufacturers to produce components.
The flaws discovered by the team are real, though they require administrative privileges to execute a cascade of actions, meaning taking advantage of them requires considerable access to the target system. The research describes some as backdoors deliberately included in the chips by Taiwanese company ASmedia, which partners with many manufacturers to produce components.
The access requirement makes these much more limited than the likes of Meltdown and Spectre, which exploited problems at the memory handling and architecture level. They’re certainly serious, but the manner in which they have been publicized has aroused suspicion around the web.
Why the extremely non-technical video shot on green screen with stock backgrounds composited in? Why the scare tactics of calling out AMD’s use in the military? Why don’t the bugs have CVE numbers, the standard tracking method for nearly all serious issues? Why was AMD given so little time to respond? Why not, if as the FAQ suggests, some fixes could be created in a matter of months, at least delay the publication until they were available? And what’s with the disclosure that CTS “may have, either directly or indirectly, an economic interest in the performance” of AMD? That’s not a common disclosure in situations like this.
(I’ve contacted the PR representative listed for the flaws (!) for answers to some of these questions.)
It’s hard to shake the idea that there’s some kind of grudge against AMD at play. That doesn’t make the flaws any less serious, but it does leave a bad taste in the mouth.
AMD issued a statement saying that “We are investigating this report, which we just received, to understand the methodology and merit of the findings.” Hard to do much else in a day.
As always with these big bugs, the true extent of their reach, how serious they really are, whether users or businesses will be affected, and what they can do to prevent it are all information yet to come as experts pore over and verify the data.
Featured Image: Fritzchens Fritz/Flickr